As a Master’s student immersed in cybersecurity frameworks, I’ve been particularly focused on CMMC 2.0. It’s more than just another set of controls, it represents a critical shift in how the Department of Defense (DoD) manages supply chain risk. For any organization looking to engage with the DIB, understanding this framework isn’t just about compliance, it’s about operational strategy.
What is CMMC 2.0?
At its core, CMMC 2.0 is the DoD’s answer to cyber vulnerabilities across its supply chain. It’s a verification program designed to ensure that defense contractors are actually protecting sensitive unclassified information. Rather than simply relying on contractors to say they’re secure, CMMC 2.0 mandates actual proof.
Here’s a high-level look at the three key levels:
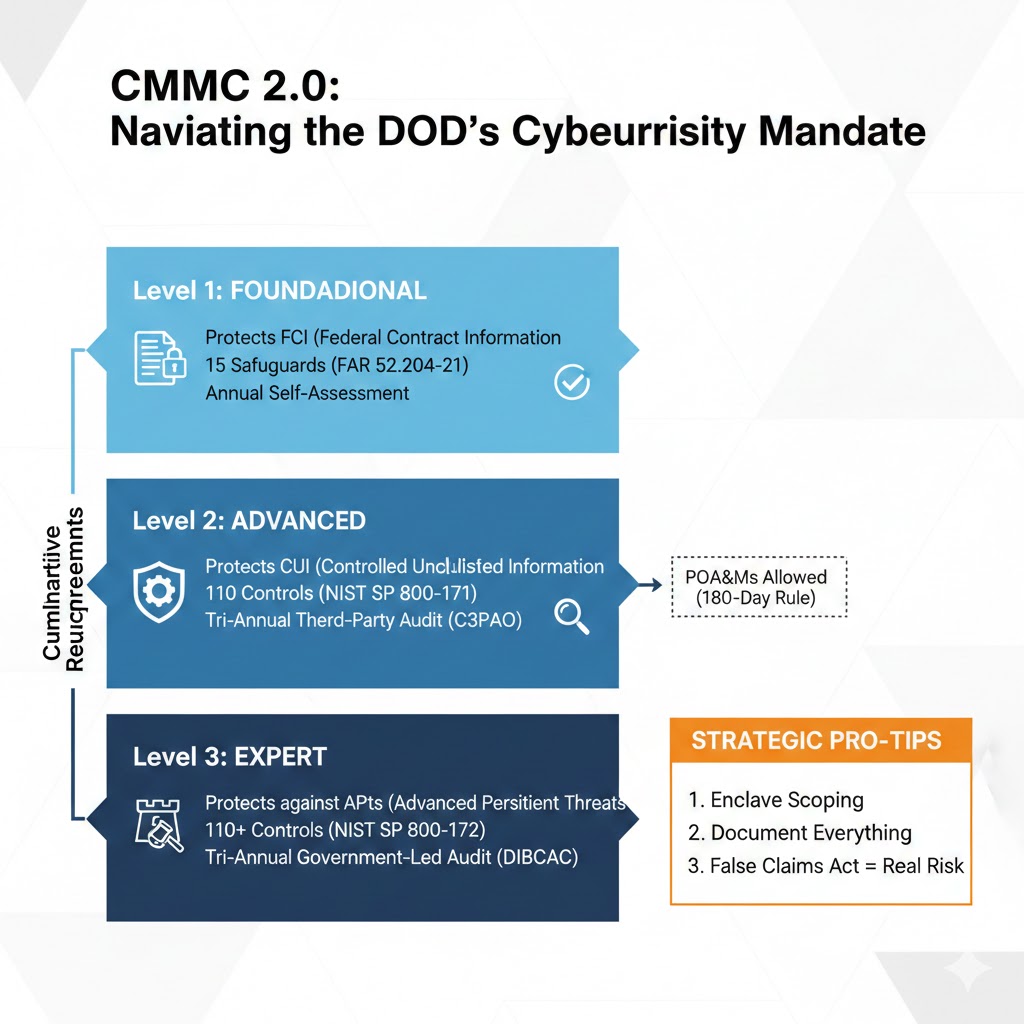
Level 1 (Foundational):
For organizations handling basic Federal Contract Information (FCI). It requires 15 controls from FAR 52.204-21, verified by an annual self-assessment.
Level 2 (Advanced):
This is the sweet spot for most of the DIB. It’s a direct implementation of the 110 controls from NIST SP 800-171 to protect Controlled Unclassified Information (CUI). Crucially, this often requires a tri-annual third-party audit (C3PAO).
Level 3 (Expert):
For the most critical programs and highly sensitive CUI, it integrates controls from NIST SP 800-172, focusing on advanced persistent threat (APT) mitigation. This level demands a tri-annual government-led audit.
My Takeaways: Strategic Insights for Future Cyber Professionals
From a student’s perspective, what truly stands out about CMMC 2.0 isn’t just the technical controls, but the strategic imperatives it imposes. Here are a few unique insights I’ve gathered:
The Enclave Strategy Scoping is Your Secret Weapon:
Trying to apply Level 2 controls to an entire company is an expensive mistake. The real pro move is aggressive scoping. Instead of securing every laptop and printer, you isolate sensitive data into a secure enclave like a hardened network segment or a specific cloud environment. This keeps your compliance footprint small. By focusing only on the systems that actually touch CUI, you dramatically reduce your attack surface and slash the costs of licenses and audits.
Documentation isn’t Just a Requirement; It’s a Weapon:
In academic settings, we learn about policies and procedures. In the real world of CMMC, meticulous documentation is your primary defense during an audit. It’s not enough to have a firewall, you need documented policies for its configuration, logs demonstrating its activity, and evidence of regular reviews. As I prepare for a career in this field, I realize this means “show your work” applies to cybersecurity operations more than anywhere else.
The False Claims Act Elevates Cyber Risk to Executive Risk:
The allowance for self-assessment in Level 1 (and potentially some Level 2 contracts) isn’t a free pass. When a senior executive signs off on an assessment, they are personally attesting to its accuracy. The implications of the False Claims Act mean that misrepresenting your cybersecurity posture isn’t just a technical oversight, it’s a legal and existential threat to the organization. This fundamentally changes the conversation around cybersecurity from an IT problem to a board-level imperative.
CMMC 2.0 is more than a framework, it’s a paradigm shift for the DIB. For those of us entering the cybersecurity field, understanding its nuances from technical implementation strategies to the legal ramifications of attestation will be crucial for building resilient defense supply chains and safeguarding national security.